My Covid-19 Experience: Navigating Work and Life During a Pandemic
The Covid-19 pandemic was an unexpected storm that turned our lives upside down. We had to adapt to new routines and cope with unforeseen challenges. One significant change was the shift to remote work, which many of us had to navigate without prior experience. Here, I’ll share my personal Covid-19 experience, focusing on how I managed my work-from-home setup and the tools that made it possible, including the best employee monitoring software, Controlio.
Adjusting to Remote Work
The initial shift to remote work was chaotic. I found myself surrounded by distractions and struggling to maintain productivity. My once orderly schedule was disrupted, and finding a new rhythm was tough. However, remote work also had its perks. No more long commutes or office politics. But to make this new setup work, I needed a solid plan and reliable tools.
Discovering the Best Employee Monitoring Software
To manage my work more effectively, … Read More
Scalable Solutions for Secure Data Management in Navigating the IoT
The Internet of Things (IoT) has revolutionized the way we interact with technology, connecting billions of devices to the internet and enabling seamless communication and data exchange. However, with this interconnectedness comes a host of cybersecurity challenges, as the sheer volume and diversity of IoT devices create vulnerabilities that can be exploited by malicious actors. This article explores scalable solutions for secure data management in the IoT landscape, addressing the challenges of data security, privacy, and integrity.
1. Understanding the IoT Ecosystem: Complexity and Vulnerabilities
The IoT ecosystem comprises a vast array of interconnected devices, ranging from consumer gadgets to industrial sensors and smart infrastructure. This section examines the complexity of the IoT landscape and the vulnerabilities inherent in its interconnected nature, including insecure communication channels, weak authentication mechanisms, and the proliferation of unpatched vulnerabilities in IoT devices.
2. Data Security in the IoT: Challenges and Considerations
Securing data in … Read More
Progressive Jackpots: How They Work and Ways to Implement Them in Gaming Apps
Hey there, fellow gaming enthusiasts! Today, we’re diving into the thrilling world of progressive jackpots. Did you know that the first progressive jackpot system was introduced in the 1980s by gaming machine manufacturer IGT? Since then, progressive jackpots have become a staple in the casino industry, offering players the chance to win life-changing sums of money with a single spin.
Understanding Progressive Jackpots
So, what exactly is a progressive jackpot? Imagine this: every time someone plays a game with a progressive jackpot, a small percentage of their bet goes into a prize pool. This pool keeps growing until someone hits the jackpot! In 2003, a lucky player made history by winning an astonishing $39.7 million jackpot on the Megabucks slot machine in Las Vegas – the largest slot jackpot ever recorded.
In the ever-evolving world of gaming, the demand for innovative solutions continues to grow, prompting companies like Boosty Labs … Read More
Ethical Considerations in the Datafication of Personal Information
In an era defined by digital transformation, the proliferation of personal data has become ubiquitous, driving innovation across industries and reshaping the way we interact with technology. This process, known as datafication, involves the conversion of various aspects of human life into quantifiable data points that can be collected, analyzed, and utilized for a myriad of purposes. While datafication offers unprecedented opportunities for innovation and progress, it also raises profound ethical considerations regarding privacy, consent, and individual autonomy.
1. Informed Consent: Navigating Complex Data Collection Practices
At the heart of the ethical debate surrounding datafication lies the issue of informed consent. As organizations collect and analyze vast amounts of personal data from individuals, ensuring that they fully understand how their data will be used and shared is paramount. However, the complexity of data collection practices often renders informed consent elusive, leaving individuals unaware of the implications of consenting to datafication. … Read More
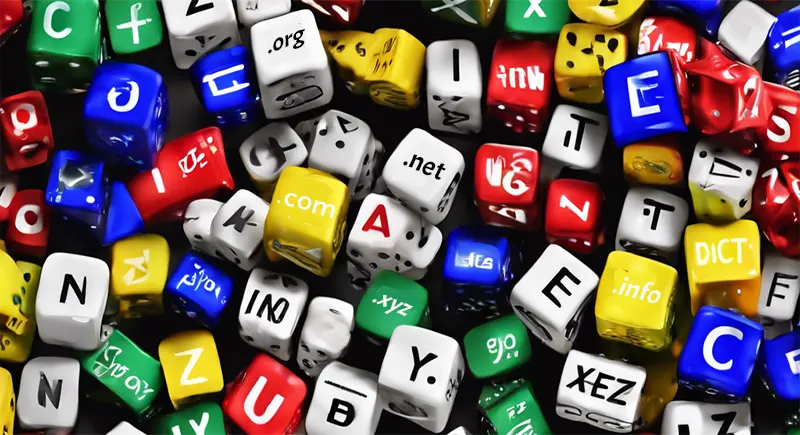
Top Examples of gTLDs
When you buy a domain name for your website from Australian domain hosts, the part after the dot (.) is called the top-level domain or TLD. For example, in the Australian domain example.com, “.com” is the TLD.
There are different types of TLDs, and one common type is the gTLD or generic top-level domain.
Let’s explore some popular examples of gTLDs and what they represent.
What are gTLDs?
As mentioned, gTLDs are top-level domains that have no restrictions on who can register them. They are “generic” in the sense that anyone, be it an individual or a company, can obtain a domain with a gTLD.
This is unlike country-code TLDs (ccTLDs) like .uk or .in, which are meant specifically for websites based in or related to the United Kingdom and India, respectively.
Due to their widespread recognition and availability, gTLDs have become the standard for most websites on the … Read More